GCP Auth is a GCP-native authentication method for GCP resources to access Infisical. It consists of two sub-methods/approaches:Documentation Index
Fetch the complete documentation index at: https://infisical-shubham-eng-984-make-secret-sharing-public-even-f.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
- GCP ID Token Auth: For GCP services including Compute Engine, App Engine standard environment, App Engine flexible environment, Cloud Functions, Cloud Run, Google Kubernetes Engine, and Cloud Build to authenticate with Infisical.
- GCP IAM Auth: For Google Cloud Platform (GCP) service accounts to authenticate with Infisical.
- Google ID Token Auth
- GCP IAM Auth
Diagram
The following sequence digram illustrates the GCP ID Token Auth workflow for authenticating GCP resources with Infisical.Concept
At a high-level, Infisical authenticates a GCP resource by verifying its identity and checking that it meets specific requirements (e.g. it is an allowed GCE instance) at the/api/v1/auth/gcp-auth/login endpoint. If successful,
then Infisical returns a short-lived access token that can be used to make authenticated requests to the Infisical API.To be more specific:- The client running on a GCP service obtains an ID token constituting the identity for a GCP resource such as a GCE instance or Cloud Function; this is a unique JWT token that includes details about the instance as well as Google’s RS256 signature.
- The client sends the ID token to Infisical at the
/api/v1/auth/gcp-auth/loginendpoint. - Infisical verifies the token against Google’s public OAuth2 certificates.
- Infisical checks if the entity behind the ID token is allowed to authenticate with Infisical based on set criteria such as Allowed Service Account Emails.
- If all is well, Infisical returns a short-lived access token that the client can use to make authenticated requests to the Infisical API.
We recommend using one of Infisical’s clients like SDKs or the Infisical Agent
to authenticate with Infisical using GCP ID Token Auth as they handle the
authentication process including generating the instance ID token for you.Also, note that Infisical needs network-level access to send requests to the Google Cloud API
as part of the GCP Auth workflow.
Guide
In the following steps, we explore how to create and use identities for your workloads and applications on GCP to access the Infisical API using the GCP ID Token authentication method.Creating an identity
To create an identity, head to your Organization Settings > Access Control > Machine Identities and press Create identity. When creating an identity, you specify an organization level role for it to assume; you can configure roles in Organization Settings > Access Control > Organization Roles.
When creating an identity, you specify an organization level role for it to assume; you can configure roles in Organization Settings > Access Control > Organization Roles. Now input a few details for your new identity. Here’s some guidance for each field:
Now input a few details for your new identity. Here’s some guidance for each field: Here’s some more guidance on each field:
Here’s some more guidance on each field:
 When creating an identity, you specify an organization level role for it to assume; you can configure roles in Organization Settings > Access Control > Organization Roles.
When creating an identity, you specify an organization level role for it to assume; you can configure roles in Organization Settings > Access Control > Organization Roles. Now input a few details for your new identity. Here’s some guidance for each field:
Now input a few details for your new identity. Here’s some guidance for each field:- Name (required): A friendly name for the identity.
- Role (required): A role from the Organization Roles tab for the identity to assume. The organization role assigned will determine what organization level resources this identity can have access to.
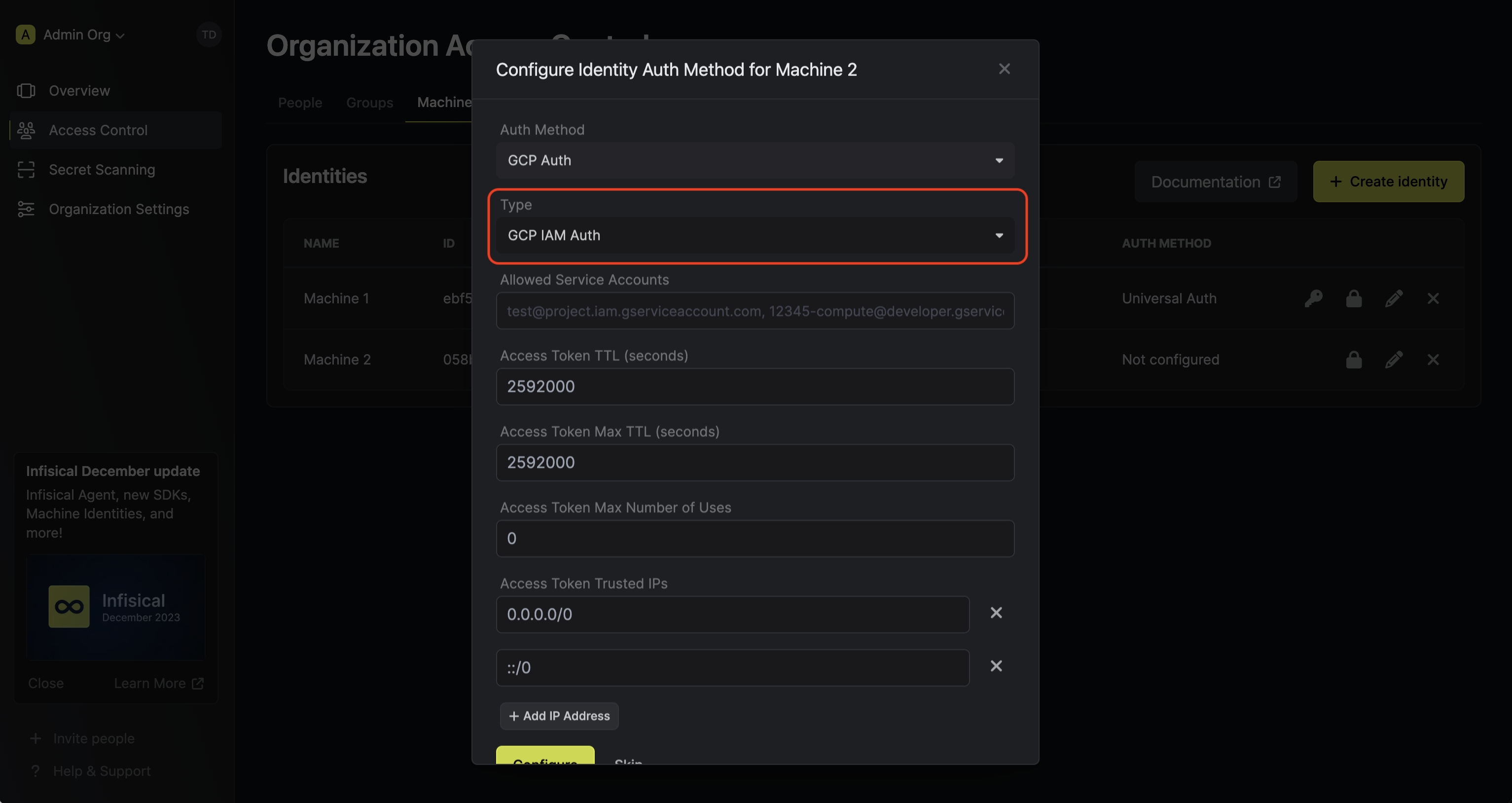
 Here’s some more guidance on each field:
Here’s some more guidance on each field:- Allowed Service Account Emails: A comma-separated list of trusted service account emails corresponding to the GCE resource(s) allowed to authenticate with Infisical; this could be something like
test@project.iam.gserviceaccount.com,12345-compute@developer.gserviceaccount.com, etc. - Allowed Projects: A comma-separated list of trusted GCP projects that the GCE instance must belong to authenticate with Infisical. Note that this validation property will only work for GCE instances.
- Allowed Zones: A comma-separated list of trusted zones that the GCE instances must belong to authenticate with Infisical; this should be the fully-qualified zone name in the format
<region>-<zone>likeus-central1-a,us-west1-b, etc. Note that this validation property will only work for GCE instances. - Access Token TTL (default is
2592000equivalent to 30 days): The lifetime for an acccess token in seconds. This value will be referenced at renewal time. - Access Token Max TTL (default is
2592000equivalent to 30 days): The maximum lifetime for an acccess token in seconds. This value will be referenced at renewal time. - Access Token Max Number of Uses (default is
0): The maximum number of times that an access token can be used; a value of0implies infinite number of uses. - Access Token Trusted IPs: The IPs or CIDR ranges that access tokens can be used from. By default, each token is given the
0.0.0.0/0, allowing usage from any network address.
Adding an identity to a project
To enable the identity to access project-level resources such as secrets within a specific project, you should add it to that project.To do this, head over to the project you want to add the identity to and go to Project Settings > Access Control > Machine Identities and press Add identity.Next, select the identity you want to add to the project and the project level role you want to allow it to assume. The project role assigned will determine what project level resources this identity can have access to.



Accessing the Infisical API with the identity
To access the Infisical API as the identity, you need to generate an ID token constituting the identity of the present GCE instance and make a request to the
/api/v1/auth/gcp-auth/login endpoint containing the token in exchange for an access token.We provide a few code examples below of how you can authenticate with Infisical to access the Infisical API.Sample code for generating the ID token
Sample code for generating the ID token
Start by making a request from the GCE instance to obtain the ID token.
For more examples of how to obtain the token in Java, Go, Node.js, etc. refer to the official documentation.Next use send the obtained JWT token along to authenticate with Infisical and obtain an access token.Next, you can use the access token to access the Infisical API
Sample request
Note that you should replace
<identityId> with the ID of the identity you created in step 1.Sample request
Request
Sample response
Response
Each identity access token has a time-to-live (TLL) which you can infer from the response of the login operation;
the default TTL is
7200 seconds which can be adjusted.
If an identity access token expires, it can no longer authenticate with the Infisical API. In this case,
a new access token should be obtained by performing another login operation.